Apple Maps Now Available in Beta on the Web: Here’s How to Try It on Your Browser

Yesterday it was made Apple Maps public beta available on the web. In other words, it is now possible to ...
WhatsApp Like Telegram, Usernames Coming Instead of Phone Numbers: What Will Change

AI generated image According to what is reported by the specialized website WABetaInfo, Whatsapp is working on a new and ...
The Energy Cost of AI: Google and Microsoft Used 24 TWh of Electricity in 2023

In today’s technology landscape, tech giants like Google And Microsoft They are not only leaders in innovation and digital services, ...
Digital Detox, 5 Tech Tips on How to “Detox” Yourself from Your Smartphone in Summer

For many people, summer is a perfect time to experience a period of digital detox (literally “digital detox”), that is, ...
5 Cases of Inventions and Discoveries Contested Among Scientists Because They Were Made Simultaneously

The inventions disputed between two or more inventors are numerous. Progress, in fact, proceeds gradually and the efforts of several ...
Microsoft Down, Computer Failures Block Planes, Hospitals and Banks: What’s Happening

In these last hours An IT glitch has blocked planes, hospitals and banks and caused computer blackouts. The cause of ...
CrowdStrike, what is the software that crashed Microsoft and PCs around the world with the “blue screen”?
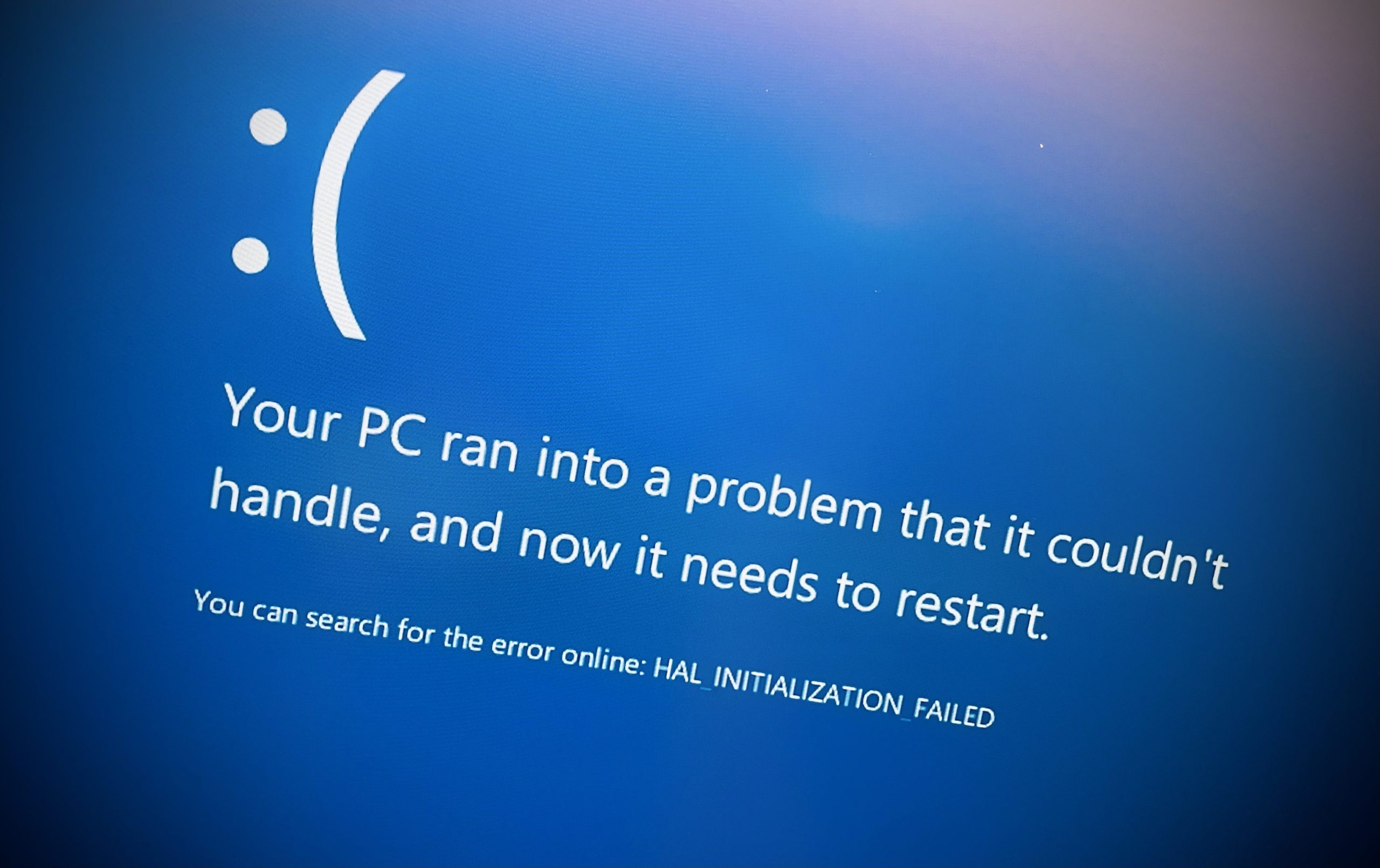
An error contained in the latest update of CrowdStrike Falcon Sensora software that is part of the CrowdStrike cybersecurity suite, ...
Anti-abandonment devices for children, how they work and which are required by law

Every now and then in Italy we return to talk about the so-called anti-abandonment devices for children. This happens especially ...
What is Spoofing, How Does It Work, and How to Protect Yourself?

The spoofing is a cyber attack in which an attacker pretends to be a trusted entity – an acquaintance of ...










