Analysts of the cybersecurity company ThreatFabric have recently discovered the existence of Brokewella new family of banking trojan malware designed to steal confidential data and obtain theFull remote access of Android devices. The “superpowers” of this type of malicious software allow cybercriminals to completely control victims' devices, potentially even stealing banking data. The installation of this malware occurs without the knowledge of the unfortunate users who, thinking they are downloading a software update from a fake Google Chrome update page, give free access to their device.
Brokewell virus: what it is and how it works
As he indicates ThreatFabric in his detailed analysis «Brokewell is a typical modern banking malware equipped with data theft and remote control capabilities.” This means, therefore, that the purpose of the malware in question is to transmit everything the user does on their Android device to cyber criminals who use it.
This new family of malware is in fact capable of steal any activity performed on a device: from the information displayed on the screen to the text typed on the keyboard, through call history, geolocation, open applications, the capture of audio material via its microphones and even the simulation of touches on the screen of the infected device.
All actions captured by the malware are then recorded and sent to the command and control serverthus completing the theft of confidential data, including banking data that is possibly available on the victim's phone.
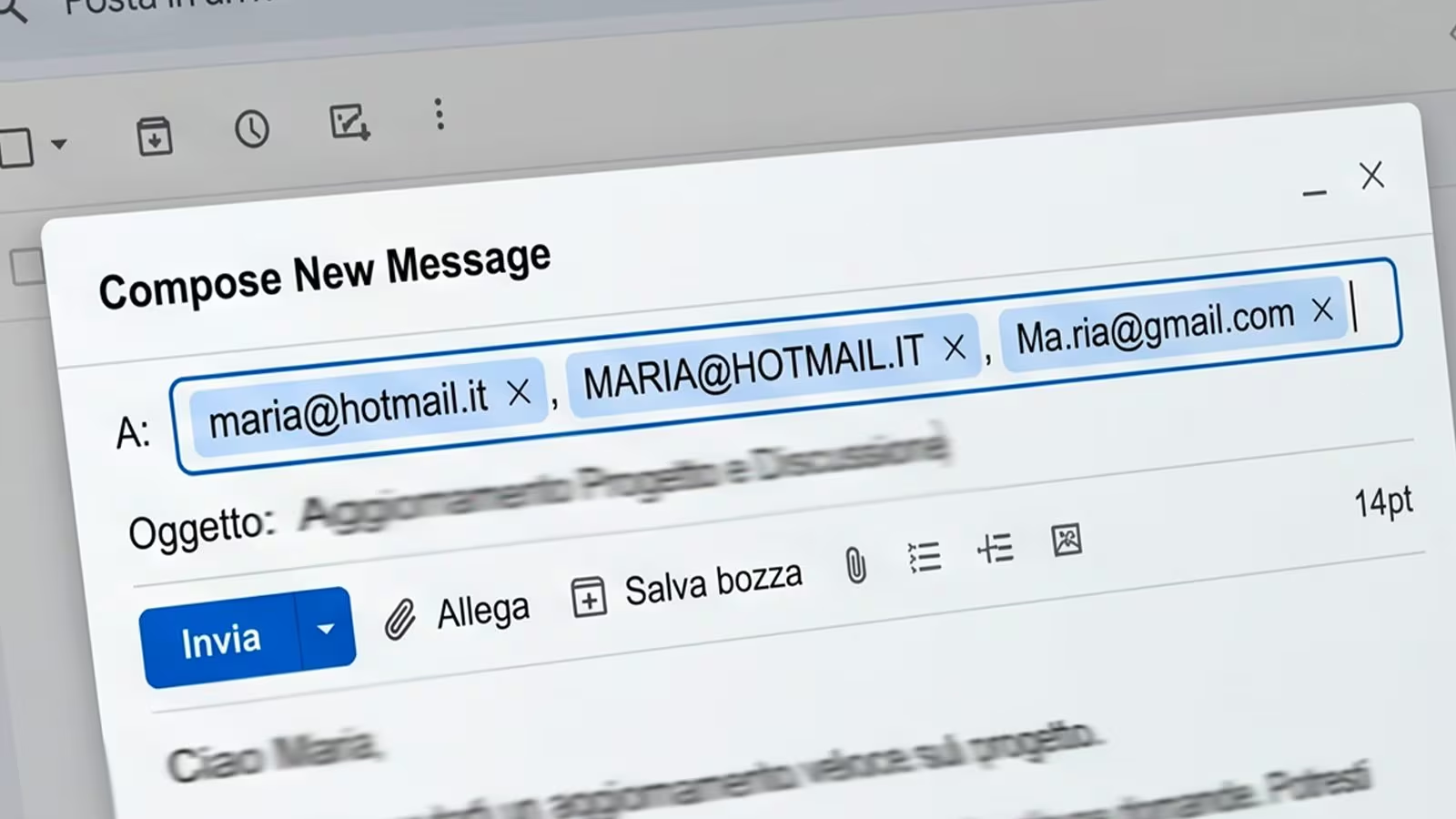
According to what was stated by the cybersecurity company mentioned above, the creator of this new family of malware would be a certain Baron Samedit Marais which, presumably, is reselling its “creation” together with a whole series of other malicious tools through a repository (i.e. an online space) called “Brokewell Cyber Labs” which, as can be seen from the following screenshot, would also offer ad hoc tools to hack PayPal, Amazon, Dropbox, Apple and American Express accounts.
How to defend yourself from the Brokewell Trojan
Since it is a particularly dangerous malware and, apparently, made quite well, being able to protecting yourself may not be that simple. At least that's what the experts say ThreatFabricwho in their analysis report:
The discovery of a new malware family, Brokewell, which implements Device Takeover capabilities from scratch, highlights the continued demand for such capabilities by cybercriminals. These actors need this functionality to commit fraud directly on victims' devices, creating a significant challenge for fraud detection tools. (…) We expect further evolution of this malware family, as we have already observed almost daily updates. Brokewell will likely be promoted on underground channels as a service for hire, attracting the interest of other cybercriminals and sparking new campaigns targeting different regions.
One thing is for sure, in the face of such “refined” and well-crafted cyber dangers, it matters keep your attention high when you are online. In the specific case of the Brokewell malware family, you need to pay attention to the page that invites you to install an update Chrome which, despite being very similar to an authentic update screen, is actually fake (as can be seen from the screenshot below). If you pressed the download button available on the fake screen, you would not download a Chrome update, but the application belonging to the malware family we have talked about so far. In fact, it is through the page in question that your device becomes infected.
To avoid contagion it is therefore essential update Chrome from the Play Store instead of external sources (this discussion, of course, applies to any other app) e keep Play Protect active on your devicewhich is the security mechanism built into Android.