An exploit kit called Coruna was initially used in targeted hacking operations traced back to a government client, but during 2025 it was also observed in campaigns conducted by different criminal groups and state actors. This was revealed by some investigations conducted by experts from the Google Threat Intelligence Group. The phenomenon highlights a known risk in the cybersecurity sector: offensive tools developed for intelligence purposes can escape original control and circulate between subjects who reuse them for malicious purposes.
Coruna is particularly sophisticated because it exploits numerous vulnerabilities in iOS systems and can compromise a device simply by tricking the user into visiting a malicious web page. Researchers also identified malware associated with this kit, called Plasmagrid, capable of stealing sensitive data and even emptying cryptocurrency wallets. The good news is that Apple has already corrected the vulnerabilities exploited by the attack system some time ago with software updates released in January 2024. The best defense tool to defend against this security flaw, therefore, is always the same: promptly install system updates.
The Coruna exploit kit: how dangerous it is
The case concerns a so-called exploit kit, i.e. a set of tools designed to automatically exploit flaws in software. To clarify, an exploit is a piece of code that takes advantage of an error or vulnerability in a program to gain unauthorized access to a system. When multiple exploits are combined into a single software infrastructure, it is called an exploit kit. Coruna belongs to this category and, according to analyzes by security researchers from the Google Threat Intelligence Group and the security company iVerify, includes several techniques to bypass protections built into the iPhone operating system.
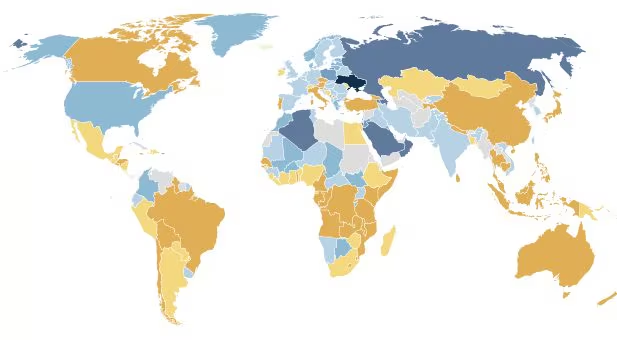
The discovery of the kit dates back to February 2025, when Google’s cyber threat intelligence team spotted it during an attempted smartphone compromise by a surveillance vendor. The operation appeared to be conducted on behalf of a government client. In the following months, the same tool reappeared in completely different contexts: first in a large-scale campaign aimed at sites frequented by Ukrainian users and attributed to a Russian espionage group identified as UNC6353, then in operations conducted by an actor of Chinese nationality, known as UNC6691, which targeted online betting platforms and cryptocurrency-related services.
This passage between different actors has fueled the hypothesis of the existence of a black market for exploits, that is, a scenario in which tools developed for government operations are subsequently resold or reused by other entities. A particularly sought after category is that of zero-days, i.e. those vulnerabilities unknown to the software producers. Since there is no patch (i.e. a corrective update) yet, these flaws can be exploited to great effect by attackers, leaving companies developing the software “zero days” to correct the situation (this is why they are called zero-day attacks). For the record, in the case of Coruna, the vulnerabilities involved were patched by Apple in January 2024 with the release of the iOS 17.3 update.
The operation of the kit is complex but the attachment mechanism can be surprisingly simple. The tools identified allow a device to be compromised also through a technique called watering hole attack. The expression takes inspiration from the animal world and, in particular, from the strategy used by some predators who wait for the right opportunity to attack their prey when they are busy drinking. In the cyber context, it refers to an attack in which hackers observe which websites an organization’s users frequent and then use one or more of these sites to distribute malware to achieve their criminal goals.
In the case of Coruna, the kit would be able to attack iPhones with five different exploit chains, exploiting a total of 23 distinct vulnerabilities. The potentially exposed devices were those with iOS versions between 13.0 (released in 2019) and 17.2.1 (released in late 2023).
Once your smartphone is compromised, malware called Plasmagrid can be installed on the device. This would be able to collect sensitive data, financial information and even access cryptocurrency wallets on the device.
How to secure your iPhone
To protect yourself from similar vulnerabilities, you must be prepared to keep iOS updated at all times. The security updates released by Apple (and, more generally, by smartphone and electronic device manufacturers) also correct the vulnerabilities exploited by exploit kits, inhibiting many attack techniques.
When it is not possible to install the latest updates, for example on very old devices, further protection is to activate isolation mode which, as Apple explains, «aadds an extreme and optional level of protection for the small number of users who (due to their identity and activity) may be the target of some of the most sophisticated digital threats directed at them personally». This advanced security feature dramatically reduces the device’s attack surfaces while limiting various features. It is not designed for everyday use by all users, but it can represent an effective barrier against sophisticated attacks, especially if you belong to categories particularly targeted by cybercriminals, such as journalists and activists.